The group, identified as Advanced Persistent Threat (APT), has been active since at least November 2013, was first discovered by American security firm Forcepoint in 2016, and has been dubbed “Bitter” and “Manlinghua” by Chinese company Qihoo 360. ” was named.
Cybersecurity analysts suspect that the group’s origins can be traced back to India and possibly state-backed, based on the location of IP addresses and language patterns observed in the attacks. Additionally, Bitter is believed to have ties to several other groups suspected to be Indian, including Patchwork, SideWinder, and Donot.
Amid cyberattacks, China’s Ministry of Foreign Affairs has consistently refrained from publicly condemning it.
Russian hacker Alexander Ermakov linked to massive Australian data breach in 2022
Russian hacker Alexander Ermakov linked to massive Australian data breach in 2022
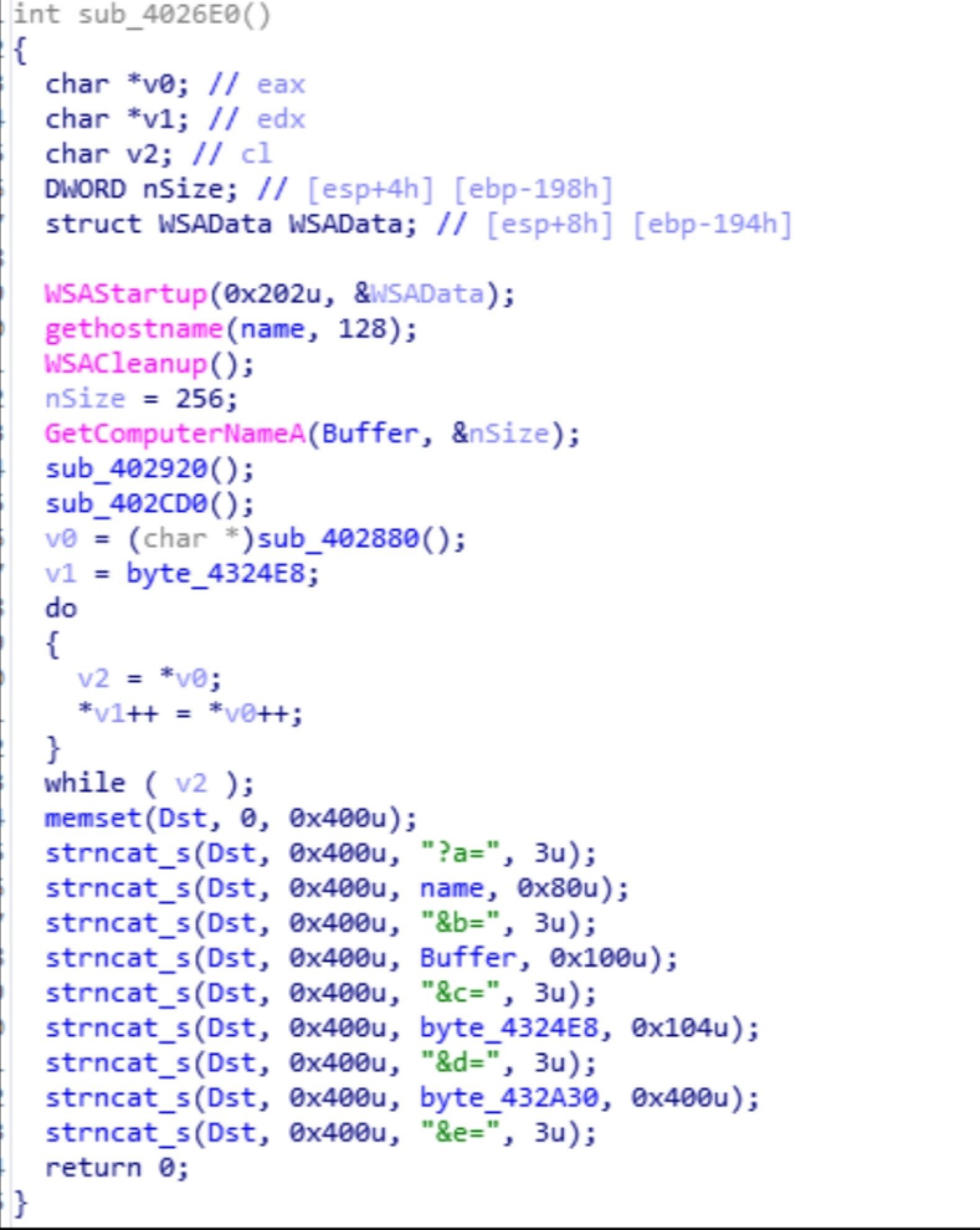
Spear phishing involves emailing a decoy document or link to a targeted individual. Once opened, the Trojan horse is deployed, downloading malicious modules, stealing data, and allowing further instructions from the attacker.
Watering hole attacks compromise legitimate websites to host malicious files or create fake websites to trap victims. It typically focuses on content that is interesting to the target audience, such as shared forum software tools.
Bitter’s operations are primarily focused on intelligence gathering, and while they do not appear to be destructive on the surface, they can lead to major information breaches with untold consequences.
According to disclosures from cybersecurity companies such as Anheng, QiAnXin, Intezer, and Secuinfra, seven attacks closely related to Bitter occurred in 2022 and eight in 2023, targeting Pakistan, Bangladesh, Mongolia, and China.
These attacks ranged from impersonating the Kyrgyz embassy to sending emails to China’s nuclear industry. The hackers also posed as military contractors providing anti-drone systems to the Bangladesh Air Force and used compromised email accounts to spread malicious files under the guise of New Year’s greetings.
“Given the widespread nature of these attacks, it is likely that such incidents continue to occur in the background,” the experts said.
“It is difficult to quantify the actual damage caused by Bitter from reported incidents. In most cases, there is little harm, but under certain circumstances, this incident could be an iceberg of potential risk.” It’s just one corner of the story.”

